---------------------------------------------------------------------------------
Explain hidden shares. How do they work?
Hidden or administrative shares are share names with a dollar sign ($) appended to their names. Administrative shares are usually created automatically for the root of each drive letter. They do not display in the network browse list.
Name of seven layers in Open System Interconnection model.
They are Application, Presentation, Session, Transport, Network, Data link, and Physical.
What is the difference between ARP and RARP?
The address resolution protocol (ARP) is used to associate the 32 bit IP address with the 48 bit physical address, used by a host or a router to find the physical address of another host on its network by sending a ARP uery packet that includes the IP address of the receiver.
The reverse address resolution protocol (RARP) allows a host to discover its Internet address when it knows only its physical address.
What is Client/Server?
Clients and Servers are separate logical entities that work together over a network to accomplish a task. Many systems with very different architectures that are connected together are also called Client/Server.
What is MAC address?
It is the 48 bit hardware address of LAN card. MAC address is usually stored in ROM on the network adapter card and it is unique.
What are the perquisites to configure server?
- LAN card should be connected:
- Root (partition on which window is installed) should in NTFS
- Server should be configured with a static IP address
How we will configure ADS?
Start ==> RUN ==> DCPROMO
How will you test LAN card?
Ping 127.0.0.1
If getting reply its fine
What are the difference between DOMAIN and WORKGROUP?
Workgroup:-
(i)Every PC is responsible for its security own.
(ii)No centralize administration
(iii)Main aim to save hardware recourse
(iv)Best suite in school, training institute, cyber café
Domain: -
(i)Server is responsible for data safety.
(ii)Centralize administration
(iii)Main aim is to secure data
(iv)Best suite in company environments
Which command is used to check the IP address of your system?
ipconfig
Which set wizard will run to do peer to peer networking in XP?
Small home and office setup wizard
Which command is used to check the physical connectivity between two computers?
Ping
What is map drive?
A special feature that will map network resource to my computer.
What is Proxy Server?
Most large businesses, organizations, and universities these days use a proxy server. This is a server that all computers on the local network have to go through before accessing information on the Internet. By using a proxy server, an organization can improve the network performance and filter what users connected to the network can access.
Which folder contains ADS installed on server?
NTDS
What is the full form of Internet?
International Networking
Which are the bootable files of 98 and XP ?
In windows98 it is command.com
In XP it is NTLDR
In which partition Linux is installed ?.
Linux doesn’t support windows file system that contain partition scheme. It (Linux) has its own file system known as ext2, and ext3. it will install only on it.In linux file system it will install on / (root) partition.
What is size of SWAP ?
It’s the hard disk space that is used as RAM for fast processing. In window it’s known as virtual memory and could be set as per retirement via this path
My Computer ==> properties ==> advance
In Linux it’s known as SWAP space and generally taken the double size of physical RAM For example if you have 256 (MB) DDR physical ram then swap space would be 512 MB.
What is full form of C.M.O.S ?
Complementary metal oxide semiconductor
How will you check ip address without using network place ?
Start ==> Run ==> Command ==>ipconfig
What is IP?
Internet Protocol (IP) is an unreliable, best effort delivery, connection-less protocol used for transmitting and receiving data between hosts in a TCP/IP network
What are the difference between hub and switch?
Hub is a layer 1 device. It will out the signal from all of its port except the one from where its insert. It is unable to detect the collision. It works on single collision and single broadcast domain.
Switch is layer 2 device. It maintains a CAM table that store the MAC address of devices attached on its port. CAM table is used to make the forwarding decision. It works on per port collision and single broadcast domain.
What is layer?
Layer is a completely logical partition of PDU (protocol data unit) process. That define how the information is travel form one computer to other over the network.
What is TCP/IP?
It is combination of two protocols TCP and IP. It is used for reliable data transfer.
What is operating system?
An operating system (sometimes abbreviated as "OS") is the program that, after being initially loaded into the computer by a boot program, manages all the other programs in a computer. It provides a platform to application software.
What is package software?
The collection of mostly used software released in package Form Company. For Example Ms-Office that contain word, power point, Excel, etc.
Full form of .co.in, .com
- COM - ".com" stands for "commercial".
- NET - ".net" stands for "network"
- ORG - ".org" stands for "organization"
- INFO - ".info" stands for "information"
- BIZ - ".biz" stands for "business".
- IN - 'IN' stands for India. The 'IN' is a 2-letter country code for India.
What is ring topology?
In a ring topology, device one connects to device two, device two connects to device three, and so on to the last device, which connects back to device one.
Which cable is used in LAN?
Generally coaxial and TP media is used in LAN networking.
What are Difference between STP and UTP?
STP cable is mostly used by IBM; it has an extra cover over each pair.
UTP cable is used in star topology. It has a single cover over all pair.
Full form of ping.
PING stand for
Packet Internet Grouper
What are the minimum requirements for xp installation?
64MB RAM
1.5GB free HDD space
233MHz minimum processor.
What are 10Base2, 10Base5 and 10BaseT Ethernet LANs?
10Base2— An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling, with a contiguous cable segment length of 100 meters and a maximum of 2 segments.
10Base5—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling, with 5 continuous segments not exceeding 100 meters per segment.
10BaseT—An Ethernet term meaning a maximum transfer rate of 10 Megabits per second that uses baseband signaling and twisted pair cabling.
What is the difference between an unspecified passive open and a fully specified passive open?
An unspecified passive open has the server waiting for a connection request from a client.
A fully specified passive open has the server waiting for a connection from a specific client.
Explain the function of Transmission Control Block
A TCB is a complex data structure that contains a considerable amount of information about each connection.
What is a Management Information Base (MIB)?
A Management Information Base is part of every SNMP-managed device. Each SNMP agent has the MIB database that contains information about the device's status, its performance, connections, and configuration. The MIB is queried by SNMP.
What is anonymous FTP and why would you use it?
Anonymous FTP enables users to connect to a host without using a valid login and password. Usually, anonymous FTP uses a login called anonymous or guest, with the password usually requesting the user's ID for tracking purposes only. Anonymous FTP is used to enable a large number of users to access files on the host without having to go to the trouble of setting up logins for them all. Anonymous FTP systems usually have strict controls over the areas an anonymous user can access.
What is a pseudo tty?
A pseudo tty or false terminal enables external machines to connect through Telnet or rlogin. Without a pseudo tty, no connection can take place.
What does the Mount protocol do?
The Mount protocol returns a file handle and the name of the file system in which a requested file resides. The message is sent to the client from the server after reception of a client's request
What is External Data Representation?
External Data Representation is a method of encoding data within an RPC message, used to ensure that the data is not system-dependent.
When were OSI model developed and why its standard called 802.XX and so on?
OSI model was developed in February1980 that why these also known as 802.XX Standard (Notice 80 means ==> 1980, 2means ==> February)
What is Full form of ADS?
Active Directory Structure
How will you register and activate windows?
If you have not activated windows XP, you can do so at any time by clicking the windows Activation icon in the system tray to initiate activation. Once you have activated windows XP, this icon disappears from the system tray.
For registration
Start ==> Run ==> regwiz /r
Where do we use cross and standard cable?
Computer to computer ==> cross
Switch/hub to switch/hub ==>cross
Computer to switch/hub ==>standard
How many pins do serial ports have?
In computer it's known as com port and could be available in 9pin or 25 pin. On router it have 60 pins.
How will check ip address on 98?
Start ==> Run ==> command ==> winipcfg
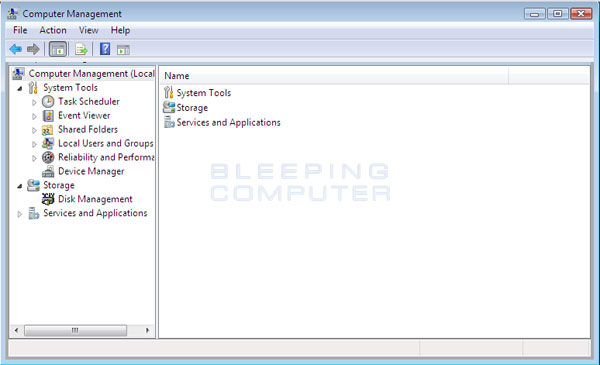
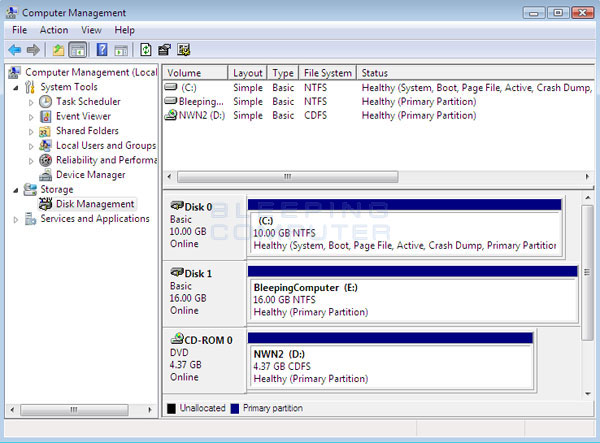
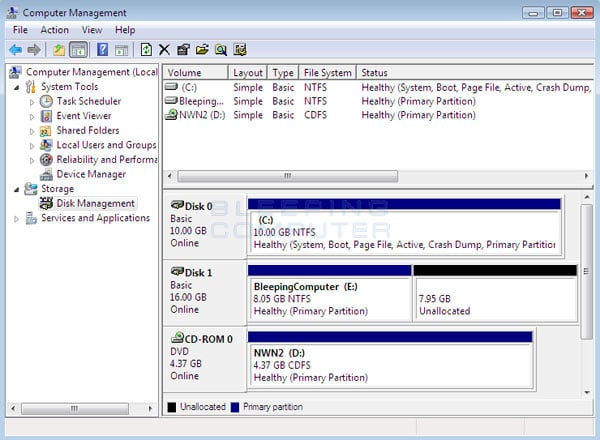
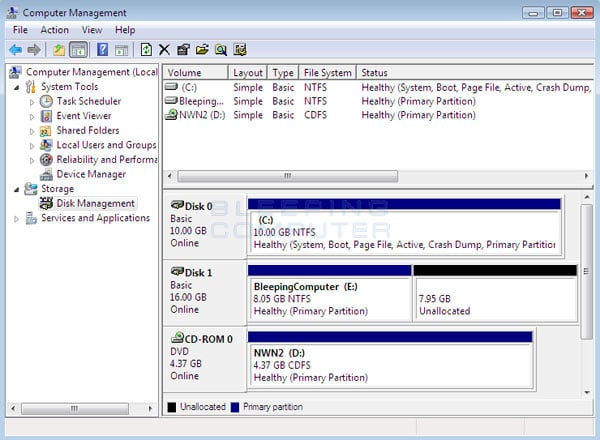
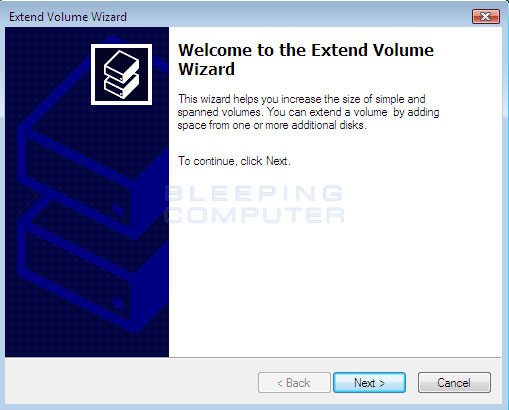
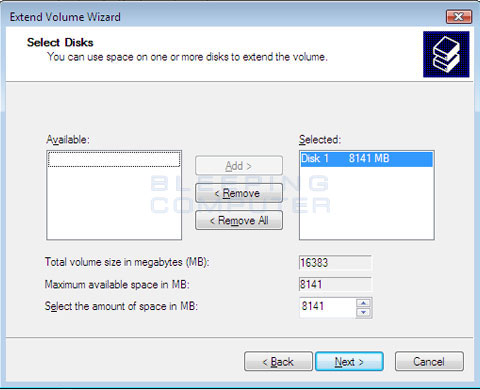
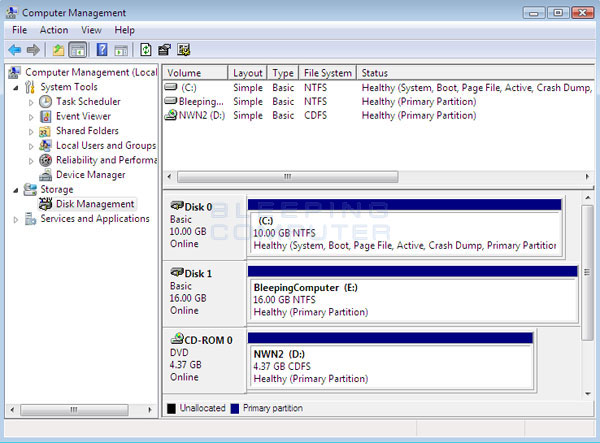
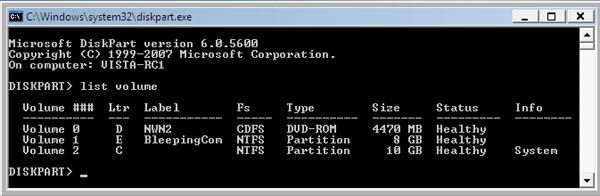
How will you make partition after installing windows?
My computer ==> right click ==> manage ==> disk management ==>
select free space ==> right click ==> New partition
What is IP?
It's a unique 32 bits software address of a node in a network.
What is private IP?
Three ranges of IP addresses have been reserved for private address and they are not valid for use on the Internet. If you want to access internet with these address you must have to use proxy server or NAT server (on normal cases the role of proxy server is played by your ISP.).If you do decide to implement a private IP address range, you can use IP addresses from any of the following classes:
Class A 10.0.0.0 10.255.255.255
Class B 172.16.0.0 172.31.255.255
Class C 192.168.0.0 192.168.255.255
What is public IP address?
A public IP address is an address leased from an ISP that allows or enables direct Internet communication.
What's the benefit of subnetting?
Reduce the size of the routing tables.
Reduce network traffic. Broadcast traffic can be isolated within a single logical network.
Provide a way to secure network traffic by isolating it from the rest of the network.
What are the differences between static ip addressing and dynamic ip addressing?
With static IP addressing, a computer (or other device) is configured to always use the same IP address. With dynamic addressing, the IP address can change periodically and is managed by a centralized network service
What is APIPA?
Automatic private IP addressing (APIPA) is a feature mainly found in Microsoft operating systems. APIPA enables clients to still communicate with other computers on the same network segment until an IP address can be obtained from a DHCP server, allowing the machine to fully participate on the network. The range of these IP address are the 169.254.0.1 to 169.254.255.254 with a default Class B subnet mask of 255.255.0.0.
What are the LMHOSTS files?
The LMHOSTS file is a static method of resolving NetBIOS names to IP addresses in the same way that the HOSTS file is a static method of resolving domain names into IP addresses. An LMHOSTS file is a text file that maps NetBIOS names to IP addresses; it must be manually configured and updated.
What is DHCP scope?
A scope is a range, or pool, of IP addresses that can be leased to DHCP clients on a given subnet.
What is FQDN?
An FQDN contains (fully qualified domain name) both the hostname and a domain name. It uniquely identifies a host within a DNS hierarchy
What is the DNS forwarder?
DNS servers often must communicate with DNS servers outside of the local network. A forwarder is an entry that is used when a DNS server receives DNS queries that it cannot resolve locally. It then forwards those requests to external DNS servers for resolution.
Which command will you use to find out the name of the pc in networks?
NSLOOKUP [192.168.0.1]
[Ip of target computer]
How will enable sound service in 2003?
By default this service remain disable to enable this service
Start ==> administrative tools ==> service ==> windows audio ==> start up type ==> automatic
How will enable CD burning service in 2003?
By default this service remain disable to enable this service
Start ==> administrative tools ==> service ==> IMAPI CD burning com service ==> start up type ==> automatic
What do you need to do that your browser will point URL www.example.com to the internal IP address 127.99.11.01?
Make changes in the hosts file in C:\WINDOWS\system32\drivers\etc
The Hosts file is looked at first before going out to the DNS (Domain Name Service) servers. you have to put the following on new lines at the end of hosts file:
127.99.11.01 example.com
127.99.11.01 www.example.com
What can you suggest to enhance testing process on windows OS?
Put shortcut to notepad.exe in SendTo folder. It is speed up work with different files like hosts, configuration files. Location of this folder is
C:\Documents and Settings\Default User\sendto.
Open it and create shortcut of notpad.exe
What is FTP?
FTP is short for File Transfer Protocol. This is the protocol used for file transfer over the Internet.
How will you make XP home the client of server 2003?
XP home edition is made only for home purpose so we can’t use it as the client. And same rule apply on windows vista editions also.
Where do you take back up from?
Click Start, point to All Programs, point to Accessories, point to System Tools, and then click Backup.
Bedside's it?
If OS support then Select Drive ==> properties ==> back up now
What is router?
Router is a device that is used to connect two different networks.
How will you configure ADS?
Start ==> Run ==> DCPROMO
Or
Start==> Configure your server ==> add/Remove a Role
What is ADS?
A central component of the Windows platform, Active Directory service provides the means to manage the identities and relationships that make up network environments.
What if this wizard (ADS) is not running?
Check the network cable it should be plugged
Check root partition it should be in NTFS
Check IP of server it should be configured statically
How will you add a client to server? /
How’s the client join a domain?
What are the client configurations?
On Server
Configure ADS (for example it’s configured with xyz.com)
On Client
Log in form local administrator account
My Computer ==> Properties ==> Computer Name ==> Change
==>Domain ==>xyz.com ==> username Administrator (of xyz.com)
Password xxxxxxxxxxx (of admin of xyz.com)
Welcome to xyz.com ==> Restart the computer
Does it necessary to use administrator account to configure the client?
Not every time but you are required a properly configured user account in domain controller security policy.
ISO stand for?
International standard organization
OSI stand for?
Open System Interconnection
What is full form DHCP and how will you configure it?
Dynamic host configuration protocol
To configure it on Server
Configure your server ==>Add/Remove a role ==>DHCP server ==>complete the wizard
Start ==> Administrative tools ==> DHCP ==>New scope ==> Wizard
Now authorized this server and do activate it
On client
Local area network ==> tcp/ip ==> obtain ip automatically
Obtain DNS automatically
What is difference between physical and logical topology?
A physical topology describes how devices are physically cabled together.
A logical topology describes how devices communicate across the physical topology
How many types of topology are available?
A
point-to-point topology has a single connection between two devices.
In a
star topology, a central device has many point-to-point connections to other devices.
A
bus topology uses a single connection or wire to connect all devices.
In a
ring topology, device one connects to device two, device two connects to device three, and so on to the last device, which connects back to device one.
How many times computer reboot when server 2000 install?
2 times.
How will you remove this error “ ntldr missing press any key to reboot the system” ?
Reboot the system with XP, ( apply also on server2003,) cd
On setup screen press to R to repair the window
Now provide the administrator password
C:\>cd f:( your cd drive latter, f is taken as the example )
f:\>cd i386
f:\>copy ntldr c:\
f:\>exit
reboot the system
Why do we do networking?
For data sharing
To accumulate hardware resource
What are the benefits of networking?
There are lots of advantages from build up a network, but the three big facts are-
File Sharing
From sharing files you can view, modify, and copy files stored on a different computer on the network just as easily as if they were stored on your computer.
Resource Sharing
Resources such as printers, fax machines, Storage Devices (HDD, FDD and CD Drives), Webcam, Scanners, Modem and many more devices can be shared.
Program Sharing
Just as you can share files on a network, you can often also share program on a network. For example, if you have the right type of software license, you can have a shared copy of Microsoft Office, or some other program, and keep it on the network server, from where it is also run
What is network?
A network is basically all of the components (hardware and software) involved in connecting computers across small and large distances.
What is networking?
A process that is describes how the network will connect.
What is topology?
A topology defines how the devices are connected. Further it is divided in physical and logical topology.
What are the differences between FAT and NTFS ?
FAT
Doesn't provide local security Provide local security
Doesn't provide disk quota Provide disk quota
Doesn't provide file compression Provide file compression
Doesn't provide other security feature Provide other security feature
Difference between XP home and XP professional ?
Feature that is not available in XP home edition
Remote Desktop
Off line file and folder
Encrypting file system
Group policy
Roaming profile
Remote installation
Joining Domain
The features listed above are only available in XP professional
Which OSI layer does IP belong?
P belongs to the Network Layer (layer 3) in the OSI model.
What is a subnet mask?
Subnet mask is a 4 byte (32 bit) number used to identify the sub-network ID and the host ID from an IP address. All the hosts in a sub-network will have the same subnet mask. E.g. 255.255.255.0, 255.255.127.0, 255.255.0.0
Where are the Windows NT Primary Domain Controller (PDC) and its Backup Domain Controller (BDC) in Server 2003?
The scheme of PDC and BDC is replaced by The Active Directory in server 2000 and further. Now all domain controllers share a multi master peer-to-peer read and write relationship that hosts copies of the Active Directory.
How can group policy be refreshed?
- Restart the server
- Leave the server ideal for 90 minute
- Run ==> gpupdate (server 2003 only)
What is LILO?
LILO stands for Linux boot loader. It will load the MBR, master boot record, into the memory, and tell the system which partition and hard drive to boot from.
I can't seem to access the Internet, don't have any access to the corporate network and on IP configuration on my address is 169.254.*.*. What happened?
The 169.254.*.* net mask is assigned to Windows machines running 98/2000/XP if the DHCP server is not available. The name for the technology is APIPA (Automatic Private Internet Protocol Addressing).
We've installed a new Windows-based DHCP server, however, the users do not seem to be getting DHCP leases off of it.
The server must be authorized first with the Active Directory.
What's the difference between local, global and universal groups?
Domain local groups assign access permissions to domain groups for local domain resources. Global groups provide access to resources in entire domains.
What's the major difference between FAT and NTFS on a local machine?
FAT and FAT32 provide no security over locally logged-on users. Only native NTFS provides extensive permission control on both remote and local files.
What is presentation layer and how it is responsible for in the OSI model?
The presentation layer establishes the data format prior to passing it along to the network application's interface. TCP/IP networks perform this task at the application layer
When were OSI model developed and why its standard called 802.XX and so on?
OSI model was developed in February1980 that why these also known as 802.XX Standard (Notice 80 means ==> 1980, 2means ==> February)
What is Full form of ADS?
Active Directory Structure
How will you register and activate windows?
If you have not activated windows XP, you can do so at any time by clicking the windows Activation icon in the system tray to initiate activation. Once you have activated windows XP, this icon disappears from the system tray.
For registration
Start ==> Run ==> regwiz /r
Where do we use cross and standard cable?
Computer to computer ==> cross
Switch/hub to switch/hub ==>cross
Computer to switch/hub ==>standard
How many pins do serial ports have?
In computer it's known as com port and could be available in 9pin or 25 pin. On router it have 60 pins.
How will check ip address on 98?
Start ==> Run ==> command ==> winipcfg
What is source route?
It is a sequence of IP addresses identifying the route a datagram must follow. A source route may optionally be included in an IP datagram header.
What is RIP (Routing Information Protocol)?
It is a simple protocol used to exchange information between the routers.
What is SLIP (Serial Line Interface Protocol)?
It is a simple protocol used for transmission of IP datagrams across a serial line.
What is Proxy ARP?
It is using a router to answer ARP requests. This will be done when the originating host believes that a destination is local, when in fact is lies beyond router.
What is OSPF?
It is an Internet routing protocol that scales well, can route traffic along multiple paths, and uses knowledge of an Internet's topology to make accurate routing decisions.
What is Kerberos?
It is an authentication service developed at the Massachusetts Institute of Technology. Kerberos uses encryption to prevent intruders from discovering passwords and gaining unauthorized access to files.
What is a Multi-homed Host?
It is a host that has a multiple network interfaces and that requires multiple IP addresses is called as a Multihomed Host.
What is NVT (Network Virtual Terminal)?
It is a set of rules defining a very simple virtual terminal interaction. The NVT is used in the start of a Telnet session.
What is Gateway-to-Gateway protocol?
It is a protocol formerly used to exchange routing information between Internet core routers.
What is BGP (Border Gateway Protocol)?
It is a protocol used to advertise the set of networks that can be reached with in an autonomous system. BGP enables this information to be shared with the autonomous system. This is newer than EGP (Exterior Gateway Protocol).
What is autonomous system?
It is a collection of routers under the control of a single administrative authority and that uses a common Interior Gateway Protocol.
What is EGP (Exterior Gateway Protocol)?
t is the protocol the routers in neighboring autonomous systems use to identify the set of networks that can be reached within or via each autonomous system.
What is IGP (Interior Gateway Protocol)?
It is any routing protocol used within an autonomous system.
What is Mail Gateway?
It is a system that performs a protocol translation between different electronic mail delivery protocols.
What is wide-mouth frog?
Wide-mouth frog is the simplest known key distribution center (KDC) authentication protocol.
What is silly window syndrome?
It is a problem that can ruin TCP performance. This problem occurs when data are passed to the sending TCP entity in large blocks, but an interactive application on the receiving side reads 1 byte at a time.
What is region?
When hierarchical routing is used, the routers are divided into what we call regions, with each router knowing all the details about how to route packets to destinations within its own region, but knowing nothing about the internal structure of other regions.
What is multicast routing?
Sending a message to a group is called multicasting, and its routing algorithm is called multicast routing.
What is traffic shaping?
One of the main causes of congestion is that traffic is often busy. If hosts could be made to transmit at a uniform rate, congestion would be less common. Another open loop method to help manage congestion is forcing the packet to be transmitted at a more predictable rate. This is called traffic shaping.
What is packet filter?
Packet filter is a standard router equipped with some extra functionality. The extra functionality allows every incoming or outgoing packet to be inspected. Packets meeting some criterion are forwarded normally. Those that fail the test are dropped.
BOOTP helps a diskless workstation boot. How does it get a message to the network looking for its IP address and the location of its operating system boot files?
BOOTP sends a UDP message with a subnet work broadcast address and waits for a reply from a server that gives it the IP address. The same message might contain the name of the machine that has the boot files on it. If the boot image location is not specified, the workstation sends another UDP message to query the server.
What is a DNS resource record?
resource record is an entry in a name server's database. There are several types of resource records used, including name-to-address resolution information. Resource records are maintained as ASCII files.
What protocol is used by DNS name servers?
DNS uses UDP for communication between servers. It is a better choice than TCP because of the improved speed a connectionless protocol offers. Of course, transmission reliability suffers with UDP.
What is the difference between interior and exterior neighbor gateways?
Interior gateways connect LANs of one organization, whereas exterior gateways connect the organization to the outside world.
What is the HELLO protocol used for?
The HELLO protocol uses time instead of distance to determine optimal routing. It is an alternative to the Routing Information Protocol.
What are the three type of routing tables and What are the advantages and disadvantages of these?
The three types of routing tables are fixed, dynamic, and fixed central.
A fixed table must be manually modified every time there is a change.
A dynamic table changes its information based on network traffic, reducing the amount of manual maintenance.
A fixed central table lets a manager modify only one table, which is then read by other devices. The fixed central table reduces the need to update each machine's table, as with the fixed table. Usually a dynamic table causes the fewest problems for a network administrator, although the table's contents can change without the administrator being aware of the change.
What is MAC address ?
The address for a device as it is identified at the
Media Access Control (MAC) layer in the network architecture. MAC address is usually stored in ROM on the network adapter card and is unique.
What is attenuation?
The degeneration of a signal over distance on a network cable is called
attenuation.
What is cladding?
A layer of a glass surrounding the center fiber of glass inside a fiber-optic cable.
What is RAID?
A method for providing fault tolerance by using multiple hard disk drives.
What is NETBIOS and NETBEUI?
NETBIOS is a programming interface that allows I/O requests to be sent to and received from a remote computer and it hides the networking hardware from applications.
NETBEUI is NetBIOS extended user interface. A transport protocol designed by Microsoft and IBM for the use on small subnets.
What is redirector?
Redirector is software that intercept
What is Beaconing?
The process that allows a network to self-repair networks problems. The stations on the network notify the other stations on the ring when they are not receiving the transmissions. Beaconing is used in Token ring and FDDI networks.
What is terminal emulation, in which layer it comes?
Telnet is also called as terminal emulation. It belongs to application layer.
What is frame relay, in which layer it comes?
Frame relay is a packet switching technology. It will operate in the data link layer.
What do you meant by "triple X" in Networks?
The function of PAD (Packet Assembler Disassembler) is described in a document known as X.3. The standard protocol has been defined between the terminal and the PAD, called X.28; another standard protocol exists between hte PAD and the network, called X.29. Together, these three recommendations are often called "triple X".
What is SAP?
Series of interface points that allow other computers to communicate with the other layers of network protocol stack.
What is subnet?
A generic term for section of a large networks usually separated by a bridge or router.
What is subnet mask?
It is a term that makes distinguish between network address and host address in IP address. Subnet mask value 0 defines host partition in IP address and value 1 – 255 defines Network address.
Describe Various Network Type
Local Area Networks Local area networks (LANs) are used to connect networking devices that are in a very close geographic area, such as a floor of a building, a building itself, or a campus environment.
Wide Area Networks Wide area networks (WANs) are used to connect LANs together. Typically, WANs are used when the LANs that must be connected are separated by a large distance.
Metropolitan Area Networks A metropolitan area network (MAN) is a hybrid between a LAN and a WAN.
Content Networks Content networks (CNs) were developed to ease users’ access to Internet resources. Companies deploy basically two types of CNs:
1.Caching downloaded Internet information
2.Distributing Internet traffic loads across multiple servers
Storage Area Networks Storage area networks (SANs) provide a high-speed infrastructure to move data between storage devices and file servers.
Advantage
Performance is fast.
Availability is high because of the redundancy features available.
Distances can span up to 10 kilometers.
Management is easy because of the centralization of data resources.
Overhead is low (uses a thin protocol).
Disadvantage of SANs is their cost.
Intranet An intranet is basically a network that is local to a company. In other words, users from within this company can find all of their resources without having to go outside of the company. An intranet can include LANs, private WANs and MANs,
Extranet An extranet is an extended intranet, where certain internal services are made available to known external users or external business partners at remote locations.
Internet An internet is used when unknown external users need to access internal resources in your network. In other words, your company might have a web site that sells various products, and you want any external user to be able to access this service.
VPN A virtual private network (VPN) is a special type of secured network. A VPN is used to provide a secure connection across a public network, such as an internet. Extranets typically use a VPN to provide a secure connection between a company and its known external users or offices.
Authentication is provided to validate the identities of the two peers.
Confidentiality provides encryption of the data to keep it private from prying eyes.
Integrity is used to ensure that the data sent between the two devices or sites has not been tampered with.